On January 29, the New York Attorney General announced an important step in the fight against spyware: Holding advertisers accountable for their payments to spyware vendors. This is a principle I’ve long endorsed — beginning with my 2003 listing of Gator advertisers (then including Apple, Chrysler, and Orbitz), and continuing in my more recent articles about advertising intermediaries funding spyware and specific companies advertising through spyware.
I’m not the only one to applaud this approach. FTC Commissioner Leibowitz recently commended the NYAG’s settlement, explaining that “advertising dollars fuel the demand side of the nuisance adware problem by giving [adware vendors] the incentive to expand their installed base, with or without consumers’ consent.” In a pair of 2006 reports, the Center for Democracy and Technology also investigated spyware advertisers, attempting to expose the web of relationships that fund spyware vendors.
The NYAG’s settlement offers a major step forward in stopping spyware because it marks the first legally binding obligation that certain advertisers keep their ads (and their ad budgets) out of spyware. In Assurances of Discontinuance, Cingular (now part of AT&T), Priceline, and Travelocity each agreed to cease use of spyware. In particular, each company agreed either to stop using spyware advertising, or to use only “adware” that provides appropriate disclosures to users, prominently labels ads, and offers an easy procedure to uninstall. These requirements apply to ads purchased directly by Cingular, Priceline, and Travelocity, as well as to all marketing partners acting on their behalf.
These important promises are the first legally-binding obligations, from any Internet advertisers, to restrict use of spyware. (Compare, e.g., advertisers voluntarily announcing an intention to cease spyware advertising — admirable but not legally binding.) If followed, these promises would keep the Cingular, Priceline, and Travelocity ad budgets away from spyware vendors — reducing the economic incentive to make and distribute spyware.
But despite their duties to the NYAG, both Cingular and Travelocity have failed to sever their ties with spyware vendors. As shown in the six examples below, Cingular and Travelocity continue to receive spyware-originating traffic, including traffic from some of the web’s most notorious and most widespread spyware, in direct violation of their respective Assurances of Discontinuance. That said, Priceline seems to have succeeded in substantially reducing these relationships — suggesting that Cingular and Travelocity could do better if they put forth appropriate effort.
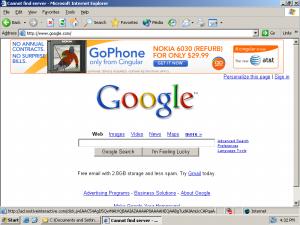
Example 1: Fullcontext, Yieldx (Admedian), Icon Media (Vizi) Injecting Travelocity Ad Into Google
 A Travelocity Ad Injected into Google by Fullcontext
A Travelocity Ad Injected into Google by Fullcontext
money
Icon (Vizi Media)
money
Yieldx (Ad|Median)
money
Fullcontext
The Money Trail – How Travelocity Pays Fullcontext
On a PC with Fullcontext spyware installed (controlling server 64.40.99.166), I requested www.google.com. In testing of February 13, I received the image shown in the thumbnail at right — with a large 728×90 pixel banner ad appearing above the Google site. Google does not sell this advertising placement to any advertiser for any price. But Fullcontext spyware placed Travelocity’s ad there nonetheless — without permission from Google, and without payment to Google.
As shown in the video I preserved, clicking the ad takes users through to the Travelocity site. The full list of URLs associated with this ad placement:
http://64.40.99.166/adrotate.php
http://ad.yieldx.com/imp?z=6&Z=728×90&s=41637&u=http%3A%2F%2Fwww.google.com…
http://ad.yieldmanager.com/imp?z=6&Z=728×90&s=41637&u=http%3A%2F%2Fwww.goog…
http://ad.yieldx.com/iframe3?jwIAAKWiAABdAwIA5soAAAAAxAEAAAAACwADBAAABgMKxQ…
http://ad.yieldmanager.com/iframe3?jwIAAKWiAABdAwIA5soAAAAAxAEAAAAACwADBAAA…
http://network.realmedia.com/RealMedia/ads/adstream_sx.ads/iconmedianetwork…
http://network.realmedia.com/RealMedia/ads/click_lx.ads/iconmedianetworks/e…
http://clk.atdmt.com/AST/go/247mancr0020000002ast/direct;at.astncr00000121;…
http://leisure.travelocity.com/RealDeals/Details/0,2941,TRAVELOCITY_CRU_354…
As shown in the URL log and packet log, Fullcontext initiated the ad placement by sending traffic to the Yieldx ad network. (Yieldx’s Whois reports an address in Hong Kong. But Yieldx is hosted at an IP block registered to Ad|Median, an ad network with headquarters near Minneapolis.) Using the Right Media Exchange marketplace (yieldmanager.com), Yieldx/Ad|Median then sold the traffic to Icon Media Networks (now Vizi Media of LA and New York), which placed the Travelocity ad. The diagram at right depicts the chain of relationships.
This placement is typical of the Fullcontext injector. I have tracked numerous Fullcontext placements, through multiple controlling servers. I retain many dozens of examples on file. See also prior examples posted to my public site: 1, 2, 3.
The Fullcontext injector falls far short of the requirements of Travelocity’s Assurance of Discontinuance. For one, users often receive Fullcontext without agreeing to install it — through exploits and in undisclosed bundles (violating Travelocity Assurance page 4, provision 11.a; PDF page 11). Furthermore, Fullcontext’s ads lack any branding indicating what adware program delivered them — violating Assurance provision 11.b, which requires such branding to appear prominently on each adware advertisement. Fullcontext’s uninstall and legacy user functions also fail to meet the requirements set out in the Assurance.
Example 2: Fullcontext and Motive Interactive Injecting Cingular Ad Into Google
 A Cingular Ad Injected into Google by Fullcontext
A Cingular Ad Injected into Google by Fullcontext
money
Motive Interactive
money
Fullcontext
The Money Trail – How Cingular Pays Fullcontext
Through the MovieInteractive ad network, Fullcontext also injects the Cingular ad into Google. See screenshot at right, taken on February 17. On a PC with Fullcontext spyware installed (controlling server 64.40.99.166), I requested www.google.com. I received the image shown in the thumbnail at right — with a prominent Cingular banner ad appearing above Google. As in the case of Travelocity, this ad appeared without permission from Google and without payment to Google. Rather, the ad was placed into Google’s site by Fullcontext spyware.
The full list of URLs associated with this ad placement:
http://64.40.99.166/adrotate.php
http://ad.motiveinteractive.com/imp?z=6&Z=728×90&s=161838&u=http%3A%2F%2Fwww.goo…
http://ad.yieldmanager.com/imp?z=6&Z=728×90&s=161838&u=http%3A%2F%2Fwww.google.c…
http://ad.motiveinteractive.com/iframe3?jwIAAC54AgD5QwMAtVQBAAIAZAAAAP8AAAAHEQAA…
http://ad.yieldmanager.com/iframe3?jwIAAC54AgD5QwMAtVQBAAIAZAAAAP8AAAAHEQAABgTud…
http://clk.atdmt.com/goiframe/21400598/rghtccin0470000088cnt/direct;wi.728;hi.90…
http://www.cingular.com/cell-phone-service/cell-phone-details/?q_list=true&q_pho…
As shown in the URL log and packet log, Fullcontext sent traffic to Motive Interactive, a Nevada ad network. Using the Right Media Exchange marketplace (yieldmanager.com), Motive Interactive sold the traffic to Cingular. The diagram at right depicts the chain of relationships. Notice that Cingular’s relationship with Fullcontext is one level shorter than the Travelocity relationship in Example 1.
Cingular should have known that this traffic was coming from spyware, because detailed information about the ad placement was sent to Cingular’s web servers whenever a user clicked a FullContext-placed ad. The packet log shows the information sent to the Atlas servers operating on Cingular’s behalf:
http://view.atdmt.com/CNT/iview/rghtccin0470000088cnt/direct;wi.728;hi.90/01?click=http:// ad.motiveinteractive.com/click,jwIAAC54AgD5QwMAtVQBAAIAZAAAAP8AAAAHEQAABgTudAIAmUcCAPqaAAC
iJAIAAAAAAAAAAAAAAAAAAAAAAKdz10UAAAAA,,http%3A%2F%2Fwww%2Egoogle%2Ecom%2F,
The first portion of the URL specifies what ad is to be shown, while the portion following the question mark reports how traffic purportedly reached this ad. (This information structure is standard for Right Media placements.) Notice the green highlighted text — telling Atlas (and in turn Cingular) that this ad was purportedly shown at www.google.com. But Atlas and Cingular should know that the www.google.com page does not sell banner ads to any advertiser at any price. The purported placement is therefore impossible — unless the ad was actually injected into Google’s site using spyware. The presence of this Google URL in Cingular’s referer log should have raised alarms at Cingular and should have prompted further investigation.
Example 3: Deskwizz/Searchingbooth and Ad-Flow (Rydium) Injecting Travelocity Ad Into True.com
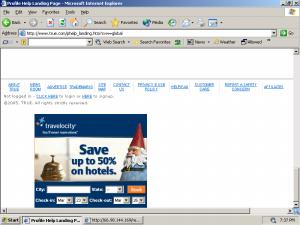 A Travelocity Ad Injected into True.com by Searchingbooth
A Travelocity Ad Injected into True.com by Searchingbooth
money
Ad-Flow (Rydium)
money
Deskwizz/Searchingbooth
The Money Trail – How Travelocity Pays Searchingbooth
Fullcontext is just one of several active ad injectors that place ads into other companies’ sites. The screenshot at right shows a injection performed by Deskwizz/Searchingbooth. In March 9 testing, I requested True.com. Deskwizz placed a large (720×300) pixel banner into the top of the page (not shown), and another into the bottom. This latter banner, shown in the thumbnail at right, promoted Travelocity. Just as the preceding examples occurred without payment to or permission from Google, this placement occurred without payment to or permission from True.com. Rather, the ad was placed into Google’s site by Deskwizz/Searchingbooth spyware.
The full list of URLs associated with this ad placement:
http://servedby.headlinesandnews.com/media/servlet/view/banner/unique/url/strip?…
http://www.uzoogle.com/indexP.php?PID=811
http://www.uzoogle.com [posted parameter: PID=811]
http://ad.ad-flow.com/imp?z=2&Z=300×250&s=118935&u=http%3A%2F%2Fwww.uzoogle.com%…
http://ad.yieldmanager.com/imp?z=2&Z=300×250&s=118935&u=http%3A%2F%2Fwww.uzoogle…
http://ad.doubleclick.net/adj/N447.rightmedia.com/B2130591.2;sz=300×250;click0=h…
As shown in the URL log and packet log, Deskwizz/Searchingbooth sent traffic to its Uzoogle ad loader, which forwarded the traffic onwards to Ad-Flow. (Ad-flow is the ad server of Rydium, a Toronto ad network.) The traffic then flowed through to the Right Media Exchange marketplace (yieldmanager.com), where it was sold to Travelocity. The diagram at right depicts the chain of relationships.
This placement is typical of Deskwizz/Searchingbooth. I have tracked a web of domain names operated by this group — including Calendaralerts, Droppedurl, Headlinesandnews, Z-Quest, and various others — that all receive traffic from and through similar banner injections. Z-quest.com describes itself as a “meta-search” site, while Uzoogle presents itself as offering Google-styled logos and branded search results. But in fact these sites all serve to route, frame, and redirect spyware-originating traffic, as shown above. I retain many dozens of examples on file. See also the multiple examples I have posted to my public site: 1, 2, 3, 4, 5.
Example 4: Deskwizz/Searchingbooth and Right Media Injecting Cingular Ad Into True.com
 A Cingular Ad Injected into True.com by Searchingbooth
A Cingular Ad Injected into True.com by Searchingbooth
money
Yield Manager / Right Media Exchange
money
Deskwizz/Searchingbooth
The Money Trail – How Cingular Pays Searchingbooth
Deskwizz/Searchingbooth also injects Cingular ads into third parties’ sites, including into True.com. The screenshot at right shows the resulting on-screen display (as observed on March 9). The screenshot depicts a Cingular ad placed into True.com without True’s permission and without payment to True.
The full list of URLs associated with this ad placement:
http://servedby.headlinesandnews.com/media/servlet/view/banner/unique/url/strip?…
http://optimizedby.rmxads.com/st?ad_type=ad&ad_size=728×90§ion=160636
http://ad.yieldmanager.com/imp?Z=728×90&s=160636&_salt=3434563176&u=http%3A%2F%2…
http://optimizedby.rmxads.com/iframe3?6B4AAHxzAgD5QwMAtVQBAAIAAAAAAP8AAAAGFAAABg…
http://ad.yieldmanager.com/iframe3?6B4AAHxzAgD5QwMAtVQBAAIAAAAAAP8AAAAGFAAABgJQF…
http://clk.atdmt.com/goiframe/22411278/rghtccin0470000088cnt/direct;wi.728;hi.90…
As shown in the URL log and packet log, Deskwizz/Searchingbooth sent traffic to the Right Media‘s Rmxads. The traffic then flowed through to the Right Media Exchange marketplace (yieldmanager.com), where it was sold to Cingular. The diagram at right depicts the chain of relationships.
Cingular should have known that this ad was appearing through spyware injections for the same reason presented in Example 2. In particular, the packet log reveals that specific information about ad context was reported to Cingular’s server whenever a user clicked an injected ad. This context information put Cingular on notice as to where its ads were appearing — including sites on which Cingular had never sought to advertise, and even including sites that do not accept advertising.
Example 5: Web Nexus, Traffic Marketplace Promoting Travelocity in Full-Screen Pop-Up Ads
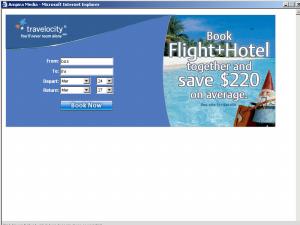 Web Nexus Promotes Travelocity Using a Full-Screen Pop-Up
Web Nexus Promotes Travelocity Using a Full-Screen Pop-Up
money
Traffic Marketplace
money
Web Nexus
The Money Trail – How Travelocity Pays Web Nexus
Although the four preceding examples all show banner ad injections, pop-up ads remain the most common form of spyware advertising. Spyware-delivered pop-ups continue to promote both Cingular and Travelocity. For example, Web Nexus is widely installed without consent (example) and in big bundles without the disclosures required by the Travelocity’s Assurance of Discontinuance. Yet Web Nexus continues to promote Travelocity through intrusive full-screen pop-ups, like that shown at right (taken on February 22). Indeed, this pop-up is so large and so intrusive that it even covers the Start button — preventing users from easily switching to another program or window.
The Travelocity ad at issue is also striking for its lack of branding or other attribution. A user who manages to move the pop-up upwards will find a small “Web Nexus” footer at the ad’s bottom edge. But this label initially appears substantially off-screen and hence unreadable. In contrast, Travelocity’s Assurance of Discontinuance (Travelocity section, page 4, provision 11.b; PDF page 11) requires that each adware-delivered advertisement be branded with a “prominent” name or icon. Because it appears off-screen, Web Nexus’s ad label cannot satisfy the NYAG’s prominence requirement. Furthermore, packet log analysis reveals that this placement is the foreseeable result of Web Nexus’s design decisions. Further discussion and analysis.
The full list of URLs associated with this ad placement:
http://stech.web-nexus.net/cp.php?loc=295&cid=9951709&u=ZWJheS5jb20v&en=&pt=3…
http://stech.web-nexus.net/sp.php/9157/715/295/9951709/527/
http://t.trafficmp.com/b.t/e48U/1172127347
http://cache.trafficmp.com/tmpad/content/clickhere/travelocity/0107/contextu…
As shown in the URL log and packet log, Web Nexus sent traffic to Traffic Marketplace (a New York ad network owned by California’s Vendare Media). The traffic then flowed through to Travelocity. The diagram at right depicts the relationships.
Example 6: Targetsaver, EasilyFound, LinkShare Promoting Cingular in Full-Screen Pop-Up Ads
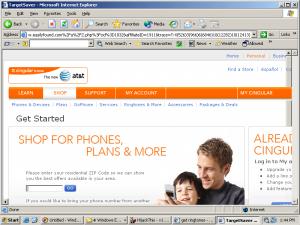 TargetSaver Promotes Cingular Using a Full-Screen Pop-Up
TargetSaver Promotes Cingular Using a Full-Screen Pop-Up
money
LinkShare
money
EasilyFound
money
TargetSaver
The Money Trail – How Cingular Pays TargetSaver
In testing of March 8, I searched for “get ringtones” at Google. I received the full-screen pop-up shown at right. This pop-up was served to me by TargetSaver spyware, widely installed consent (example) and with misleading and/or hidden disclosures (1, 2). These installation practices cannot meet Cingular’s duties under its Assurance of Discontinuance (Cingular section, page 4, provision 14.a; PDF page 18).
The full list of URLs associated with this ad placement:
http://a.targetsaver.com/adshow
http://www.targetsaver.com/redirect.php?…www.easilyfound.com%2Fa%2F2.php…
http://www.easilyfound.com/a/2.php?cid=1032
http://www.easilyfound.com/a/3.php?cid=1032
http://click.linksynergy.com/fs-bin/click?id=MCVDOmK0318&offerid=91613.100…
http://www.cingular.com/cell-phone-service/cell-phone-sales/free-phones.js…
As shown in the URL log and packet log, TargetSaver sent traffic to EasilyFound. EasilyFound then forwarded the traffic on to LinkShare, a New York affiliate network, which sent the traffic to Cingular.
Cingular should have known that a partnership with EasilyFound would entail Cingular ads being shown through spyware. EasilyFound describes itself as “a metacrawler search engine.” But in my extended testing, EasilyFound widely buys spyware-originating traffic and sends that traffic onwards to affiliate merchants (Cingular among others). I have previously described this general practice in multiple articles on my public web site. I have also publicly documented this very behavior by EasilyFound specifically. In May 2006 slides, I showed EasilyFound buying traffic from Targetsaver and sending that traffic onwards to LinkShare and Walmart. I even posted an annotated packet log and traffic flow diagram. My slides have been available on the web for approximately ten months. Yet, by all indications, this affiliate remains in good standing at LinkShare and continues the same practices I documented last year.
According to Whois data, EasilyFound is based in Santa Monica, California, although EasilyFound’s Contact page gives no street address.
The preceding six examples are only a portion of my recent records of spyware-originating ads from Cingular and Travelocity. I retain additional examples on file. My additional examples include additional banner injections, additional pop-ups, additional traffic flowing through Cingular’s affiliate program (LinkShare), and traffic flowing through Travelocity’s affiliate program (Commission Junction).
In my extended testing during the past two months, I have recorded only a single example of Priceline ads shown by spyware. That placement occurred through Priceline’s affiliate program, operated by Commission Junction.
The Assurances of Discontinuance reflect the remarkable size of the advertising expenditures that triggered the New York Attorney General’s intervention.
| Cingular Wireless (AT&T) | Priceline | Travelocity | |
| Amount spent with Direct Revenue | At least $592,172 | At least $481,765.05 | At least $767,955.93 |
| Duration of Direct Revenue relationship | April 1, 2004 through October 11, 2005 | May 1, 2004 through February 24, 2006 | July 1, 2004 through April 15, 2006 |
| Number of ads shown | At least 27,623,257 | At least 6,142,395 | At least 2,103,341 |
| Knowledge of Direct Revenue’s practices | “Even though Cingular was aware of controversy surrounding the use of adware and was aware, or should have been aware, of Direct Revenue’s deceptive practices, including surreptitious downloads, Cingular continued to use Direct Revenue.” | “Priceline knew that consumers had downloaded Direct Revenue adware without full notice and consent and continued to receive ads through that software.” | “Travelocity was aware that Direct Revenue had … been the subject of consumer complaints that Direct Revenue had surreptitiously installed its software on consumers’ computers without adequate notice.” |
| Additional factors listed by NYAG | “Some of Priceline’s advertisements were delivered directly to consumers from web servers owned or controlled by Priceline.” | ||
| Payment to New York | $35,000 of investigatory costs and penalties | $35,000 of investigatory costs and penalties | $30,000 of investigatory costs and penalties |
These three advertisers alone paid more than $1.8 million to Direct Revenue — approximately 2% of Direct Revenue’s 2004-2005 revenues. See detailed Direct Revenue financial records.