Spyware vendors are trying to clean up their images. For example, Zango settled a FTC investigation, then last week sued PC Tools for detecting and removing Zango software. Meanwhile, Integrated Search Technologies (makers of a variety of software previously widely installed without consent) introduced a new “Vomba” client that even received “provisional” TRUSTe Trusted Download certification.
But these programs’ core designs are unchanged: They still track user behavior, still send browsing to their central servers, and still show pop-up ads — behaviors users rightly disfavor due to serious effects on privacy and productivity.
Putting aside users’ well-known dislike for pop-ups, these programs also continue to interfere with standard online advertising systems. In particular, these programs show ads that overcharge affiliate merchants — especially by claiming commission on organic traffic merchants would have received anyway. This article presents six specific examples, followed by analysis and strategies for enforcement.
The Self-Targeting Scam and an Initial Example: Zango, Roundads, and Performics Claiming Commissions on Blockbuster’s Organic Traffic
Putting spyware vendors’ practices in the best possible light, they perform a comparative advertising function — offering a competitor when a user browses a merchant’s site. But suppose a spyware vendor instead shows a “competitor” that is actually just a commission-earning link to the very site the user had specifically requested. Then, if the user buys from that merchant (through either the original window or the new pop-up, in general), the merchant has to pay a commission to the spyware vendor (or its advertiser or affiliate).
For concreteness, consider the events shown in the screenshot at right and in video. On May 13, my automated testing system browsed Blockbuster. Observing the requested traffic to Blockbuster, Zango opened a popup sending traffic to Roundads.com. Roundads redirected to Performics and then back to Blockbuster. To a typical user, this pop-up is easy to ignore — just a second copy of the Blockbuster site, which users had requested in the first place. But the pop-up has serious cost implications for Blockbuster: If the user signs up with Blockbuster, through either window, then Blockbuster concludes it should pay a $18 commission to Roundads via Performics. That’s a sham: Were it not for Zango’s intervention, Blockbuster could have kept the entirety of the user’s subscription fee, without paying any commission at all.
Zango’s activity here doesn’t even meet the definition of advertising (“attracting public attention to a product or business”). After all, the user was already at Blockbuster — and hence can’t be said to have been “attract[ed]” to that site by Zango’s action.
Unless Blockbuster installs Zango’s software and runs its own tests, Blockbuster is likely to conclude (mistakenly) that Roundads has provided a bona fide lead to a new customer. Indeed, since Blockbuster’s preexisting web site visitors are likely to “convert” to buyers at a high rate (compared to visitors who only arrive thanks to advertising), Blockbuster’s advertising metrics (and Performics’ tracking measurements) are likely to consider Roundads an unusually high-quality affiliate thanks to Roundads’ likely high conversion rate. Blockbuster might even pay Roundads a bonus — when in fact this Roundads traffic is worthless.
URL log of the traffic at issue:
http://tvf.zango.com/showme.aspx?…CD=www.blockbuster.com…
http://ads.roundads.com/ads/clickcash.aspx?keyword=.blockbuster.com
http://clickserve.cc-dt.com/link/tplclick?lid=41000000005307215&pubid=…
https://www.blockbuster.com/signup/rp/regPlan/p.25216/c.firstMonth999F…
For more on these self-targeting pop-ups, targeting merchants’ sites with their own affiliate links, see my earlier The Effect of 180solutions on Affiliate Commissions and Merchants (2004).
On these facts, Blockbuster might reasonably blame Roundads — the entity that purchased the traffic from Zango and put in motion the self-targeting scheme. Investigating Roundads’ identity, Blockbuster will notice Roundads.com’s footer — which states that Roundads is one and the same as Thermo Media / Affiliate Fuel, which credit reporting agency Experian acquired in April 2005. (Update, May 22: Joey Flores, Director of Operations for Affiliate Fuel, wrote to me to report that Roundads has no affiliation with Affiliate Fuel, Thermo Media, or Experian. Joey suggests that Roundads “‘borrowed’ from [Thermo Media’s] site design … and their designers got a little copy happy, including [copying] our copyright information on[to] their site.”)
Blockbuster might also blame Performics. Performics specifically touts its affiliate network as offering “cost-effective” advertising. But in this example, the cost was a total waste, yielding no benefit whatsoever. Performics further promises “quality affiliates” — an important benefit to merchants who might not otherwise know which affiliates to accept. But in this instance, by all indications Performics failed to protect Blockbuster from Roundads’ bad actions and improper charges.
Finally, Blockbuster might blame Zango — whose pop-up generating software made it remarkably easy for Roundads to target Blockbuster’s organic traffic.
Example 2: Vomba, Ccg360, Lynxtrack (Hydra Network), Adrevolver (Blue Lithium) Claiming Commissions on Blockbuster’s Organic Traffic
Blockbuster’s online advertising is widespread, and the preceding example is but one of many schemes that charge Blockbuster commission it ought not have to pay. This section shows another.
In the screenshot shown at right, reflecting testing of May 11, my automated testing system requested the Blockbuster site. Vomba spyware observed that I was at Blockbuster, and sent traffic to Ccg360 (purportedly Nelson Cheung of Markham, Canada). Ccg360 redirected to Lynxtrack.com (Hydra Network of Beverly Hills, California), which redirected to Adrevolver (BlueLithium of San Jose, California) and finally back to Blockbuster.
As in the prior example, the net effect was to claim commission on Blockbuster’s organic traffic. If the user signs up with Blockbuster, Blockbuster will pay a commission to the sequence of companies that forwarded the Vomba-originating traffic. But had those parties not intervened with that pop-up, Blockbuster would still have closed the sale — without incurring a commission expense. So as in the prior example, this is self-targeting, charging Blockbuster a commission without providing any bona fide value in return.
URL log of the traffic at issue:
http://services.vombanetwork.com/vomba/popup.php
http://blockbuster.med.ccg360.com
http://www.lynxtrack.com/afclick.php?o=3318&b=zm00z1tf&p=11566&l=1&s=med
http://track.adrevolver.com/service.php/16520/1893/11566
https://www.blockbuster.com/signup/s/reg/p.26715/pc.blwm9.99/r./
Example 3: Vomba and LinkShare Claiming Commissions on Netflix’s Organic Traffic
Netflix has repeatedly promised to sever ties with spyware vendors, even claiming that incidents that I and others observed were “unique and random.” But through its LinkShare affiliate program, Netflix continues to get ripped off by spyware — needlessly paying commissions to receive the same kind of traffic Netflix long since promised to reject. This section and the three that follow shows four separate examples of such traffic.
In testing of April 11, my automated testing system browsed Netflix. AutoTester found traffic flowing from Vomba to LinkShare, then back to Netflix. URL log:
http://services.vombanetwork.com/vomba/popup.php
http://click.linksynergy.com/fs-bin/click?id=9SOCNdxbJKg&offerid=78684…
http://www.netflix.com/Signup?mqso=60187019&ls_sourceid=9SOCNdxbJKg-O9…
Example 4: Look2me, MyGeek (AdOn Network), Tcshoppingdeals, Apluswebdeals, and LinkShare
In testing of April 25, my automated testing system browsed Netflix. AutoTester found traffic flowing from Look2me (from Minnesota-based NicTech Networks) (widely installed without consent) to MyGeek (AdOn Network of Phoenix, Arizona) to Tcshoppingdeals (purportedly of Buffalo, New York) to Apluswebdeals (location unknown) to LinkShare, then back to Netflix. See screenshot at right and video. URL log:
http://www.ad-w-a-r-e.com/cgi-bin/UMonitorV2
http://url.cpvfeed.com/cpv.jsp?p=110250&ip=…&url=http://www.netflix….
http://www.tcshoppingdeals.com/r/link.php?id=12
http://www.a-pluswebdeals.com/visit/featured/?id=6
http://click.linksynergy.com/fs-bin/click?id=7XxjiVPyR/A&offerid=78684…
http://www.netflix.com/Signup?mqso=60187019&ls_sourceid=7XxjiVPyR_A-Mp…
Example 5: Web Nexus, Mediatraffic, Ccg360, and LinkShare
In testing of May 12, my automated testing system browsed Netflix. AutoTester found traffic flowing from Web Nexus (widely installed without consent) to Mediatraffic (one-and-the-same as Integrated Search Technologies and Vomba) to Ccg360 (purportedly Nelson Cheung of Markham, Canada) to LinkShare, and back to Netflix. See screenshot at right. URL log:
http://stech.web-nexus.net/cp.php?loc=295&cid=…
http://stech.web-nexus.net/mtraff.php/9951709/295/527/…
http://cpvfeed.mediatraffic.com/feed.php?ac=1239&kw=netflix&ip=…
http://cpvfeed.mediatraffic.com/redir.php?ac=1239&sac=&dat=…
http://netflix.med.ccg360.com
http://click.linksynergy.com/fs-bin/click?id=kic1Ixnq*SQ&offerid=…
http://www.netflix.com/Signup?mqso=60187019&ls_sourceid=kic1Ixnq.SQ-D…
Example 6: Zango, Roundads, and LinkShare
In testing of May 20, my automated testing system browsed Netflix. AutoTester found traffic flowing from Zango to Roundads to LinkShare and back to Netflix. See screenshot, video, and URL log:
http://tvf.zango.com/showme.aspx?…CD=www.netflix.com…
http://ads.roundads.com/ads/dvd.aspx?keyword=.netflix.com/Register
http://click.linksynergy.com/fs-bin/click?id=AnCa4QMGFR4&offerid=786…
http://www.netflix.com/Signup?mqso=60187019&ls_sourceid=AnCa4QMGFR4-…
In each of these four Netflix examples, spyware sent traffic to LinkShare and then onwards to Netflix — all predicated on users first requesting Netflix directly. So as in the two Blockbuster examples, the spyware provides no bona fide advertising benefit. Instead, the spyware vendors simply claim payments from Netflix without providing any service in return — a glaring reason why Netflix should refuse to pay them. Aside from reducing wasteful advertising spending, Netflix might also want to sever these relationships because the underlying spyware imposes serious costs on consumers: Sneaking onto users’ computers, reducing performance, and diminishing both reliability and privacy.
Netflix might reasonably blame LinkShare for the actions of these affiliates. LinkShare specifically touts its “high quality network” with “better affiliates,” whereas these affiliates are the very opposite of high quality. Furthermore, LinkShare prominently claims its service is “cost-efficient” — even as these examples entail Netflix paying for traffic it could have received for free.
The preceding five examples are only a portion of my recent records of spyware advertising fraud and of other spyware advertising. My AutoTester collects dozens of examples per day, and I’ve documented literally hundreds of rogue affiliates during the past year — including dozens of affiliates through each of Commission Junction, LinkShare, and Performics, as well as various affiliates using smaller networks. Any affiliate merchant without a specific plan for detecting and blocking spyware-originating traffic is virtually certain to be receiving — and paying for — this bogus self-targeting spyware-originating traffic.
The clearest effect of self-targeting pop-ups is to overcharge merchants. Self-targeting pop-ups ask merchants to pay affiliate commissions on their organic traffic — traffic they should receive for free, thanks to advertising in other media, word of mouth, and repeat buyers. But if merchants fail to take action to protect themselves, they needlessly pay commissions on this organic traffic. Merchants then also pay affiliate network fees and, often, affiliate manager fees too — making the waste that much larger.
Secondarily, self-targeting pop-ups skim commissions from other affiliates. Consider a bona fide rule-following affiliate sending traffic to a targeted merchant. If a spyware self-targeting pop-up intercedes to drop its own affiliate cookies, it overwrites the cookies of the initial affiliate. Affiliate merchants pay commissions on a “last cookie wins” basis — so the first affiliate gets nothing, even though its link truly sent the user to the merchant’s site and actually put the sale in motion. (Examples: 1, 2, 3, 4)
But self-targeting does have beneficiaries. The clearest beneficiaries are the spyware vendors that show self-targeting pop-ups — whether showing these ads directly (with the spyware vendor acting as an affiliate) or indirectly (with some affiliate buying spyware traffic and sending it onwards to a network and a merchant). The resulting revenues fund spyware vendors’ infections, installations, and other expenses.
At least in the short run, self-targeting also benefits affiliate networks. Affiliate networks typically charge merchants a percentage of each commissionable sale. So the more commissions a merchant pays out, the higher the revenues of the merchant’s network. Self-targeting pop-ups convert non-commissionable organic traffic into supposedly-commissionable supposedly-affiliate-originating traffic — expanding networks’ fee base. In the long run, self-targeting fraud could reduce merchants’ interest in affiliate marketing, but in the short run it provides networks with additional revenue. This conflict surely explains at least a portion of networks’ failure to effectively eliminate self-targeting spyware. (Further discussion.)
Nonetheless, I’ve long thought that self-targeting and other spyware traffic present a substantial opportunity for networks seeking to offer increased value to sophisticated merchants. A savvy network could stand behind the quality of its affiliates, exercising real diligence in catching fraud and in protecting merchants from the risk of wasteful, unnecessary payments. Networks can implement protections more efficiently and at lower cost than merchants, because networks can kick out affiliates across their entire network, rather than merely from a single a single merchant’s program. That said, to date the largest three affiliate networks all still receive substantial spyware-originating traffic, including self-targeting traffic.
 Revenue Counterfactual
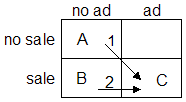
Revenue CounterfactualThe self-targeting profit opportunity ultimately arises out of mismeasurement of merchants’ own traffic. Networks’ tracking systems encourage merchants to consider the counterfactual labeled #1 in the diagram at right — comparing the sales they made (point C in the diagram) against the supposed counterfactual of not paying commissions and hence not receiving the specified sales (point A). That’s the right comparison for many kinds of advertising, but in these self-targeting examples, it’s entirely misguided. Here, the only appropriate comparison is #2 — comparing the sale that was made with payment of the specified commission (C), versus the very same sale without any commission (B). The difference is stark: In #1, the merchant is pleased to have made a sale at a reasonable marketing expense. But in #2, the true state of affairs, the merchant is paying out commissions without any business benefit whatsoever.
In Netflix’s 2007 Q1 earnings call, CFO Barry McCarthy noted that Netflix’s recent “word-of-mouth subscriber growth was weak.” There are multiple plausible explanations for that change, but advertising fraud is an important additional factor to consider: In the examples set out above, Netflix would mistakenly pay Look2me, Vomba, Web Nexus, and Zango even if a consumer in fact signed up thanks to a word-of-mouth recommendation rather than as a result of those vendors’ advertising. With marketing costs already consuming more than 23% of Netflix’s revenues, any reduction seems both overdue and welcome.
What will Netflix, Blockbuster, and other affiliate merchants do in response to these examples? One immediate action item is to sever their ties with the specific affiliates I have identified. Merchants could also demand repayment of any commissions previously paid out — a challenging task with small affiliates, but probably possible for some larger affiliates.
More generally, merchants must decide how to protect themselves from the many cheating affiliates not reported here. As usual (1, 2), I think the answer is auditing and enforcement. Merchants can run tests themselves, hire a consulting service (like AffiliateFairPlay), or build an automating testing system to find violations. But ignoring these scams is unpalatable because inaction means wasting merchants’ advertising budgets, penalizing rule-following affiliates, and helping support spyware vendors.