Not every “anti-spyware” program is what it claims to be. Some truly have users’ interests at heart — identifying and removing bona fide risks to privacy, security, stability, or performance. Others resort to a variety of tricks to confuse users about what they’re getting and why they purportedly need it.
This article reports the results of my examination of anti-spyware software from C-NetMedia. I show:
- Deceptive advertising, deceptive product names, and deceptive web site designs falsely suggest affiliation with security industry leaders. Details.
- The use of many disjoint product names prevents consumers from easily learning more about C-Net, its reputation, and its practices. Details.
- High-pressure sales tactics, including false positives, overstate the urgency of paying for an upgraded version. Details.
Note that C-NetMedia is unrelated to the well-known technology news site CNET Networks. Details.
Deceptive advertising, deceptive product names, and deceptive web site design falsely suggest affiliation with security industry leaders.
Some C-NetMedia products are marketed using practices, keywords, labels, and layouts that falsely suggest they come from security industry leaders. This suggestion comes from both the actions of C-Net itself, as well as from the actions of C-Net’s marketing partners.
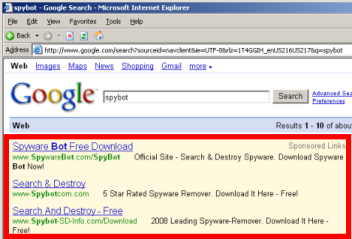
Consider the top three ads for a Google search for “Spybot”, a popular early anti-spyware program (full name “Spybot Search & Destroy”). As shown at right, the top three ads each specifically mention “Spybot” — the first two, in directory names; the third, in its domain name. Furthermore, all three ads also include the distinctive and original phrase “Search & Destroy” that specifically describes the genuine Spybot product. Yet in fact each of these three ads takes users to the unrelated site spywarebot.com (emphasis added) (screenshots: 1, 2, 3). Clicking the first ad immediately takes a user to spywarebot.com via the ClickBank advertising network. As to the second and third ads, traffic flows through independent “landing page” sites which in turn show ClickBank links to promote Spywarebot. These landing pages are hosted on the deceptively-named domains named spybot-sd-info.com and www-spybotcom.com — each further (but falsely) suggesting an affiliation with the genuine “spybot” product.
C-NetMedia partners similarly fill top ad spots for a search for “Ad-Aware”, another well-known anti-spyware program. The top ad promotes C-Net’s adwarealert.com — a name particularly likely to confuse users because the ad’s title and domain differ from the user’s request by just a single letter. The first ad takes the user to adwarealert immediately, while the second ad takes users to a www-ad-ware.com landing page which also promotes adwarealert.com (again via ClickBank).
Other deceptive C-NetMedia partners pervade search results for spyware-removal search terms. See e.g. “Spybot-free.com” using distinctive “Spybot” “Search & Destroy” marks to promote C-Net’s spywarebot.com. See also C-Net’s Registrysmart.com advertising with ad title “Microsoft Antispyware” in Google results for searches on “Microsoft Spyware”. Because the Registrysmart ad title touts “Microsoft Antispyware”, users might reasonably think the ad will yield an official Microsoft site that actually provides the free “Microsoft Antispyware” product. But in fact the link leads only to a C-Net site with paid products.
C-NetMedia may claim that these ads were placed by affiliates. But the actions of these affiliates are prominent — occurring on search terms as well-known as “Spybot” and “Ad-Aware.” These actions are also longstanding: My October 2006 False and Deceptive Pay-Per-Click Ads shows that some of these ads have continued for more than a year. Furthermore, these affiliates act for C-Net’s benefit, and C-Net has the right and ability to monitor them, to oversee their activities, and to limit their efforts as it sees fit. Finally, FTC litigation confirms that companies can be liable for the actions of their affiliates and marketing partners. See e.g. US v. APC Entertainment (advertiser liable for sexually-explicit unsolicited commercial email sent by its affiliates), In the Matter of Zango, Inc. (advertising software company liable for nonconsensual and deceptive installations of its software by its partners), In the Matter of Direct Revenue LLC (same).
C-NetMedia’s involvement in these advertising practices is heightened by C-Net’s own selection of product names. C-Net, not its affiliates, chose product names so close to established market leaders — names that invite consumer confusion. C-Net furthers the confusion by calling its products “official” (e.g. “The Official Ad-Ware Client“, emphasis added) when there is no meaningful sense in which C-Net’s products are more “official” than any other. Indeed, when users arrive at C-Net sites after requesting similarly-named better-known competitors, C-Net’s offerings are exactly not the official products users specifically requested by name.
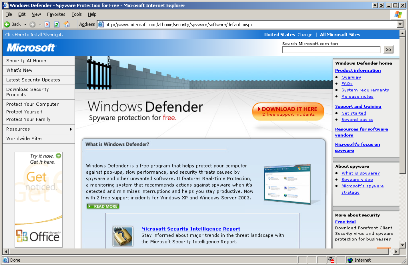
Some C-Net sites are also deceptive in that their titles and graphic design falsely suggest they are an official part of Windows. Consider antispyware.com. The site’s heading presents the generic title “AntiSpyware For Windows” — without mentioning any company name or showing any other prominent indication that the product is not actually part of Windows. Furthermore, antispyware.com shares numerous graphic design elements with official Microsoft sites: Like official Microsoft sites, antispyware.com features a broad blue bar across the top of the page, bold white type at top-left with smaller white type at top-right, a grey navigation bar down the left edge (with thin black lines as section separators, and with simple black text), a grey nav bar down the right edge (with broad grey bars to separate sections, and with blue bulleted text), a grey background, a skewed 3D rendering of a product screen at page center, and a vivid colored bubble at top-center, linking to a product download. See the two screenshots below — antispyware.com on the left, and the official Microsoft Windows Defender download page on the right. These many visual similarities make it especially likely that a user at antispyware.com will mistakenly believe the site is an official Microsoft offering.
 |
 |
|
|
C-NetMedia’s Antispyware.com
|
Microsoft Windows Defender
|
Some C-NetMedia sites give users the false impression that they are bona fide informational sites rather than commercial advertisements. For example, Remover.org presents itself as a general-purpose spyware information site, but Remover.org actually promotes only one product — C-Net’s “AntiSpyware For Windows.” Furthermore, Remover.org claims to have “one goal and one purpose: to win the war on spyware” — suggesting a non-commercial purpose, when in fact Remover charges a fee for its removal program. The totality of these practices suggests that a user at Remover.org may reasonably think he is viewing an ordinary informational site and/or a source of unbiased reviews, when in fact the site is a C-Net advertisement.
Hindering Consumer Investigations through Use of Numerous Product Names and Domains
C-Net uses exceptionally many product names and domain names. My analysis indicates that the following products and domains all come from C-NetMedia:
| Site | Whois | IP Address | Trademark |
| adware.pro | Whois-Proxy | 72.32.100.197 | |
| ad-warealert.com | Domains By Proxy (GoDaddy) | 72.32.242.170 – C-Netmedia | 77047467 – November 20, 2006 – C-Netmedia |
| adwarealert.com | Domains By Proxy (GoDaddy) | 72.32.29.230 | 77047467 – November 20, 2006 – C-Netmedia |
| adwarearrest.com | Syber Corporation 8400 East Prencitce Avenue, Ste 1500 Greenwood Village CO 80111 |
72.32.134.197 | |
| adwarebot.com | Domains By Proxy (GoDaddy) | 72.32.242.171 – C-Netmedia | |
| antispyware.com | Domains By Proxy (GoDaddy) | 72.32.26.195 | 77073855 – December 30, 2006 – C-Netmedia |
| antispywarebot.com | Domains By Proxy (GoDaddy) | 72.32.48.186 | 77047469 – November 20, 2006 – C-Netmedia |
| errorkiller.com | C&C Networks 3630 County Ct S Mobile, AL 36619 |
72.32.242.171 – C-Netmedia | 77047443 – November 20, 2006 – C-Netmedia |
| errorsmart.com | Domains By Proxy (GoDaddy) | 73.32.26.195 | |
| errorsweeper.com | Domains By Proxy (GoDaddy) | 73.32.48.186 | 77047440 – November 19, 2006 – C-Netmedia |
| evidenceeraser.com | Domains By Proxy (GoDaddy) | 73.32.29.230 | 77073969 – December 31, 2006 – C-Netmedia |
| free-pc-repair.com | Ofer Shoshani 747 Durshire Way Sunnyvale, CA 94087 |
72.32.100.197 | |
| free-registrysmart.com | Domains By Proxy (GoDaddy) | 72.32.242.171 – C-Netmedia | 77047441 – November 20, 2006 – C-Netmedia |
| macrovirus.com | Domains By Proxy (GoDaddy) | 72.32.242.171 – C-Netmedia | |
| malwarebot.com | Domains By Proxy (GoDaddy) | 72.32.242.169 – C-Netmedia | 77047470 – November 20, 2006 – C-Netmedia |
| privacycontrol.com | Domains By Proxy (GoDaddy) | 73.32.48.186 | 77073857 – December 31, 2006 – C-Netmedia |
| privacycontrols.com | Domains By Proxy (GoDaddy) | 73.32.48.186 | 77073859 – December 31, 2006 – C-Netmedia |
| regclean.com | Domains By Proxy (GoDaddy) | 73.32.48.186 | |
| regrecall.com | Domains By Proxy (GoDaddy) | 73.32.90.213 | |
| registrybot.com | Domains By Proxy (GoDaddy) | 72.32.242.169 – C-Netmedia | 77047445 – November 20, 2006 – C-Netmedia |
| registryclear.com | Bruce Cope 3630 County Ct S Mobile, AL 36619 |
72.32.134.197 | |
| registrysmart.com | PrivacyPost (Dotster) | 73.32.29.230 | 77047441 – November 20, 2006 – C-Netmedia |
| regsweep.com | Domains By Proxy (GoDaddy) | 73.32.26.195 | 77047438 – November 19, 2006 – C-Netmedia |
| remover.org | Domains By Proxy (GoDaddy) | 72.32.26.195 | |
| restore-pc.com | Domains By Proxy (GoDaddy) | 73.32.29.230 | |
| spywarebot.com | Domains By Proxy (GoDaddy) | 73.32.134.197 | |
| spywareremover.com | C&C Networks 3630 County Ct S Mobile, AL 36619 |
64.49.219.215 |
The United States Patent and Trademark Office’s Trademark Search provides the brunt of my evidence that the listed sites are associated with C-Netmedia. Other evidence comes from the 73.32.242.168-175 network block that C-Net uses at Rackspace. (Rackspace also hosts all of the other listed C-Net sites. The 64.49.219.215 server is indeed a Rackspace server, despite its distant IP address.) My conclusion is bolstered by the many other similarities among these sites, including their common substantive theme, structure, layout, registration method, and advertising relationships and suppliers. Furthermore, the sites’ programs are largely similar — with identical detections, false-positives, and user interfaces.
An ordinary user would face substantial difficulty in determining that a given site is operated by C-NetMedia or in finding C-Net’s contact information. At a few of the sites, a user would at least find a street address in Whois. But the other domains all lack useful Whois data. Furthermore, while the listed web sites offer email and/or chat support, they all lack a phone number, mailing address, or even a legal name or place of incorporation. A user seeking to send a formal complaint therefore has no clear means to do so. Savvy users might notice a reference to C-NetMedia within a program’s license agreement. But these references appear only in the licenses shown by programs’ installers — not in the license agreements linked from the corresponding web sites. So these references to C-Net are especially hard to find after a user has already received C-Net software.
A user who manages to identify the C-Net company name, e.g. from trademark applications, is still substantially stymied in learning more about the company. The name “C-NetMedia” immediately suggests an association with CNET Networks, Inc., the well-known news site at www.cnet.com. In fact C-NetMedia and CNET Networks are entirely unrelated. But by choosing a name that matches an existing company, C-Net hinders attempts to learn more about its practices: Searches for “C-Net” overwhelmingly yield references to CNET Networks.
C-Net’s use of many names brings valuable benefits to C-Net but real costs to users: The numerous names prevent users’ unfavorable views of specific C-Net products (examples: 1, 2, 3, 4, 5) from easily spreading to other C-Net products. If C-Net had only a single product, users searching for that product would easily find the complaints of prior dissatisfied users. But by shifting from name to name, C-Net can abandon product names with unfavorable coverage, in each instance starting fresh with a new name. In this regard, C-Net’s approach is strikingly similar to Direct Revenue’s use of dozens of company and product names.
It seems C-Net sometimes uses the name 2squared to describe its offerings. The 2squared.com site claims to be the maker of at least some of C-Net’s products (including ErrorSweeper and RegClean). While C-Net’s trademark applications list one address in Mobile, Alabama (590 B Schillinger Road South, Suite 8), 2squared provides the adjacent suite 10.
C-Net’s trademark applications all list Erik Mv. Pelton as their attorney of record. Mr. Pelton’s tm4smallbiz.com site indicates that he is a bona fide trademark attorney with an office in Arlington, Virginia.
High-Pressure Sales Tactics and False Positives
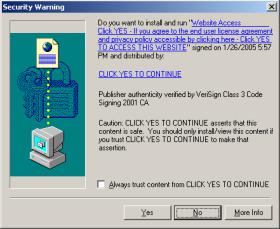
Once a user installs C-NetMedia’s free trial software, C-Net resorts to high-pressure tactics to encourage users to make a purchase.
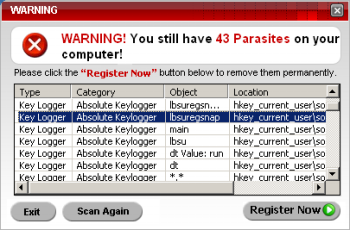
I tested C-Net’s SpywareBot on a clean PC running Windows XP with no service packs,. My test PC was supplemented only by the ordinary analysis tools I use to study spyware and adware infections. SpywareBot detected Regsnap, my registry change-tracking tool, as the “Absolute Keylogger.” Bold red “Warning” messages repeatedly alerted me to the supposed “43 parasites” on my computer, and a “toast”-style slider arose from the bottom-right corner of my screen. Perhaps this was just an ordinary false positive — a mistake that any security program can make. But C-Net’s error was unusually self-serving in that C-Net requires users to pay a fee — in this case $19.95 — before removing any of the items it detects.
C-Net’s many products mean extended further investigation would be required to fully determine the effectiveness and error rates of C-Net’s various programs. Due to the seriousness of the advertising practices described above, I have chosen to post this article without fully testing for such false positives or other deficiencies across all of C-Net’s programs and across a variety of test computers. I will update this article to link to any such research performed by others.
Other Anomalous Marketing Practices: Affiliate Programs, Certifications, and Logos
C-NetMedia’s marketing programs are striking in their generosity: C-Net offers its affiliates 70% commissions on users’ purchases. Such large commissions tend to suggest that charges to users bear little relationship to the underlying cost of providing the service. In particular, when a user arrives at C-Net’s site through an affiliate link, at least 70% of the user’s payment goes towards marketing costs. But if marketing receives 70% of revenue, relatively little remains to fund product design or other core business functions. A user might be better off with a free product — such as the free products with names nearly identical to the names C-Net selected.
 C-NetMedia sites systematically and prominently tout certifications that are substantially irrelevant to the true attributes of C-Net software. For example, C-Net’s Adwarealert site boasts a McAfee HackerSafe logo. When this logo appears on a site offering security software, a user might reasonably think the logo means the site’s software will keep the user safe from hackers. But in fact HackerSafe signifies nothing of the kind: HackerSafe has merely checked the Adwarealert web server for a set of known security problems. C-Net’s use of the HackerSafe certification thus has the tendency to deceive, i.e. to leave users with an untrue impression of the certification’s significance.
C-NetMedia sites systematically and prominently tout certifications that are substantially irrelevant to the true attributes of C-Net software. For example, C-Net’s Adwarealert site boasts a McAfee HackerSafe logo. When this logo appears on a site offering security software, a user might reasonably think the logo means the site’s software will keep the user safe from hackers. But in fact HackerSafe signifies nothing of the kind: HackerSafe has merely checked the Adwarealert web server for a set of known security problems. C-Net’s use of the HackerSafe certification thus has the tendency to deceive, i.e. to leave users with an untrue impression of the certification’s significance.
Update (February 14, 11:30am): I notice that McAfee has withdrawn HackerSafe certification of C-NetMedia sites. C-NetMedia sites now show blank space where the logo previously appeared.
Adwarealert also features a Microsoft “Certified for Windows Vista” seal. Microsoft’s certification list confirms that Adwarealert did receive this certification. But it seems Adwarealert does not truly qualify for this certification because Adwarealert violates rule 1.11 of the Microsoft certification requirements, namely the requirement that a certified program comply with all applicable guidelines from the Anti-Spyware Coalition. The ASC’s Risk Model negatively characterizes incomplete or inaccurate identifying information; obfuscation; and misleading, confusing deceptive or coercive messaging or false claims to induce users to take action. By failing to readily provide accurate contact information, by using misleading product names, and by reporting false positives with a request for payment, Adwarealert violates each of these requirements. I therefore conclude that Adwarealert is ineligible for the “Certified for Windows Vista” certification.
C-NetMedia’s sites also feature unsubstantiated claims of product benefits. C-Net sites feature the following logos: “Guaranteed – 100% No Adware or Spyware”, “#1 Most Advanced Privacy Software”, “#1 Registry Cleaner”, “100% Safe and Secure”, “Total Privacy Protection,” “Most Advanced Anti-Spyware Detection,” and “World’s #1 Spyware Remover.” None of these claims contains, references, or links to any substantiation, documentation, or other supporting details. Some of these claims are presented in graphical form, i.e. in logos that appear to be endorsements or certifications. But C-Net gives no indication of any bona fide third party offering these endorsements; instead, the graphics seem to be C-Net’s own creation.
![]()




![]()
My analysis shows ample room for online advertising and security vendors to better protect users from C-NetMedia’s deceptive advertising practices:
- Google and other search engines could block the widespread deceptive ads from C-NetMedia and its marketing partners. C-Net and its partners have continued these practices for more than a year. Google claims to be tough on malware, and Google does exclude some harmful organic search results. But Google has been ineffective in removing the false and deceptive ads shown above, among many others, despite ample complaints from users and security researchers.
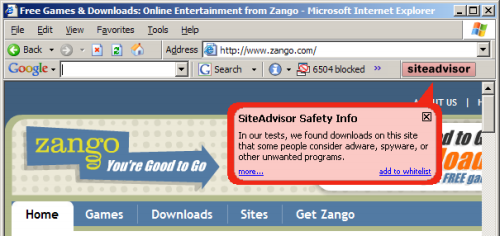
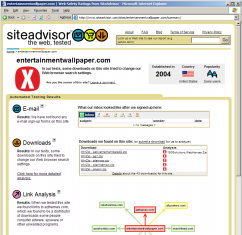
- McAfee could remove its Hacker Safe certification from C-NetMedia sites. At present, the McAfee logo gives users the false impression that McAfee endorses C-Net and the McAfee vouches for the effectiveness of C-Net’s software. I gather neither is truly the case. Indeed, McAfee’s HackerSafe certifies some C-Net sites at the same time that McAfee’s SiteAdvisor characterizes rates those same sites as red. In my view, the SiteAdvisor rating better describes the view of security experts and better serves typical users. (Disclosure: I serve as a member of the Board of Advisors of McAfee SiteAdvisor.) (Update, February 14, 11:30am: McAfee has withdrawn HackerSafe certification of C-NetMedia sites.)
- Microsoft could withdraw its Certified for Windows Vista certification on the basis of C-NetMedia’s violations of various ASC rules, as cited above. Anticipating this kind of harmful marketing practices, Microsoft’s certification rules provide ample basis for excluding C-Net on the basis of its deceptive advertising. Microsoft’s concern should be particularly acute because C-Net copied the layout and format of the Microsoft Antispyware site, because C-Net marketing partners trade on Microsoft’s brand name and product names, and because C-Net products worsen the experience of Windows users (i.e. by charging a fee for security software, when Microsoft provides similar software for free).
- ClickBank could eject C-NetMedia from ClickBank’s affiliate network due to the pattern and practice of false and misleading ads placed by ClickBank affiliates in their promotion of C-Net offers. ClickBank’s Client Contract specifically prohibits fraudulent, deceptive, false or misleading information in advertising messages (clause 7.n.), and Clickbank reserves the right to immediately suspend violators (9.d.). But at present, C-NetMedia seems to remain a ClickBank clent in good standing.
Thanks to security researcher Janie Whitty for references on C-NetMedia’s trademark registrations.
 TrustWatch certifies 180solutions as a “verified secure” site
TrustWatch certifies 180solutions as a “verified secure” site
