Installation practices occupied center stage at last week’s CNET Download.com‘s anti-spyware conference. Many of the companies whose installation practices I’ve criticized attempted to defend those practices or deflect attention from them. But their explanations and excuses don’t stand up to critical examination.
Does Claria Target Kids? Take Two…
At the CNET conference, I showed my slides of Claria’s misleading ads on kids sites. The audience seemed to think the slides are pretty damning: Claria shows an ad that looks like a Windows dialog box, though it’s not; Claria offers a clock-synchronizing program (which Windows XP users don’t need); Claria installs software with just two clicks; and Claria doesn’t show a license until after the user accepts the installation. All this, on sites targeted at kids — sites with privacy policies that say so, in case the cartoon graphics, simple language, and underlying content (often cartoon video games) weren’t clear enough.
Claria’s CEO, Jeff McFadden, responded in part by claiming that the Ezone site (the example I focused on) isn’t really targeted at kids:
“… There’s a second thing that was mentioned, that this is a kids site. I’m not sure what homework was done on this, because there’s an IDC report that says that online gaming sites, the average age of people who visit those sites is 29. I don’t know if anyone has done a demographic study of this particular site. I was shocked to find that even the Neopets web site that my daughters at home use quite frequently has a very large constituency of housewives that use the site. So we do not ‘target’ kids sites. … ”
–conference archive, session 2 recording (MP3), from 1:05:00 to 1:12:38 (excerpt – WindowsMedia), in response to my question at 55:50 to 57:50 (excerpt). See also panelists’ responses at 57:50 to 1:05:00 (excerpt).
IDC may be right that the average age of gaming site visitors is 29. But I doubt demographics are similar at cartoon video game sites like Ezone. With titles like “Beetle Junior” and “Turtle Bay,” it’s hard to think the sites could retain a major adult audience.
What would it take to convince Jeff that the Ezone site really does cater to kids, and that it isn’t an appropriate place to solicit new installations of Claria’s advertising software? Last month I posted several other examples of Claria ads on (what I claim to be) kids sites — not just Ezone, but also a site called Fingertime Games (“lunar mouse house,” “junk food jack” and other games). Today I’m adding one more, which I think is even more clearly targeted at kids. For starters, the site is called Kidzpage — its very name a play on “kids.” Its title bar and “welcome” text both say it’s “for children.” Its advertisement pitch specifically says it’s “for kids and adults … family and students … school-aged children along with the ‘grown-ups’ who supervise them.” It’s linked from Yahooligans (Yahoo for kids). Can anyone seriously dispute that users obtained at such a site will include kids who didn’t know what they were getting, and who couldn’t reasonably consent?
Beyond targeting kids, there’s plenty more wrong with this Claria installation method. See my earlier write-up for discussion of fake-user-interface, unneeded programs, and failure to show a license until after installation occurs. See also Eric Howes‘s Adware Installations of 2005, showing other Claria installations with similar shortcomings.
Ask Jeeves’ Problems: Non-consensual Installations, Semi-consensual Installations
Installation practices seem to be a question that IAC CEO Barry Diller doesn’t fully understand, or at least doesn’t care to talk about. In an earnings call last week, he said AJ “doesn’t have an issue with either spyware or adware.” But more than denying that AJ faces exposure here, Diller didn’t even want to discuss the matter. He continued: “It is an issue, obviously, but it is not our issue. And that’s that. Next question, please?”
Diller is right that the AJ toolbars aren’t either spyware or adware (as I use the terms). After all, the AJ toolbar doesn’t obviously collect much information about what users do (though I don’t fully understand all of AJ’s transmissions). And the AJ toolbar doesn’t show the annoying pop-ups common to most “adware.” (That said, AJ’s toolbar leads users to web pages with lots of PPC ads syndicated from Google. So if some AJ installations are wrongful, remember that Google revenues are ultimately funding AJ’s activities. Google staff tell me they’re “looking into it.”)
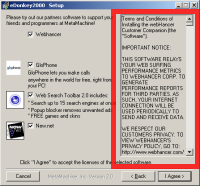
But Diller is wrong to so quickly conclude AJ has no problem here, merely because AJ doesn’t make spyware or adware. If AJ software is becoming installed through security holes w/ no notice or consent (it is), and if AJ is offering payments to those who perform these wrongful installations, AJ has a problem no matter how praiseworthy AJ’s software may be. Similarly, if AJ is installing without showing or even referencing a license, while using euphemisms that fail to properly disclose even the most general effects of the programs to be installed (again all true), AJ has a lot to improve. Same if the AJ license agreement is buried at page 48 of a license agreement users aren’t even shown unless they specifically request it (see Kazaa installer).
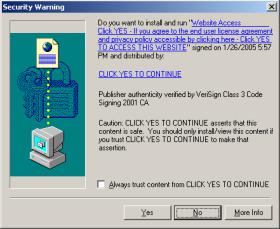
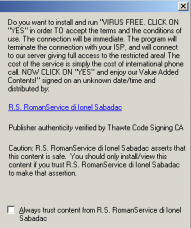
The basic legal theory — clearly articulated in the NYAG’s complaint against Intermix — is that users ought to control what software runs on their computers. So installations are only proper when they occur with user consent, after clear and straightforward disclosures. Omit the disclosures, or phrase them so euphemistically that users can’t reasonably understand, then the software installation becomes a trespass.
I don’t always agree with Marquette professor Eric Goldman. (In particular, I can’t agree with his calls for narrow liability for actions of distributors and advertisers. This seems like a recipe for unaccountability and for rewarding bad actors. Eric’s approach would encourage “adware” vendors to look the other way when their software is installed wrongfully, and would give a free pass to those who advertise through software installed improperly.) But interestingly Eric and I seem to see AJ the same way — the key question being whether AJ’s installation disclosure and consent is up to par.
180solutions Continues to Become Installed Without Any Consent At All
Representatives from 180solutions made the sensible decision not to claim, within the official CNET conference sessions, that their programs install only with consent. After all, I had screenshots and videos providing the contrary.
But in a video interview made mere minutes before, 180solutions COO Daniel Todd told Dow Jones Marketwatch that “180solutions does not install software on people’s computers without consent.” Only upon further pressing by the interviewer does Todd back-peddle, admitting that some 180 distributors install 180 software with “no consent” or without (what Todd considers) adequate consent.
So Todd admits that some 180 installs are nonconsensual. Yet 180’s web site continues to claim that its software is “permission based” and “only downloaded with user consent.”
Which one is right? My November and March videos show nonconsensual 180 installations in great detail. (I’ll post still more videos in the coming weeks, as to 180 as well as Direct Revenue, eXact Advertising, and many others.) So Todd’s ultimate admission is accurate. Not so for the “only … with … consent” promises on 180’s web site.
Todd later stated that 180 has 7,000 to 10,000 distributors. That’s a huge number — it underscores the practical difficulty of 180 performing meaningful oversight of what its distributors are doing. With so many installation “partners” and so little enforcement or quality control, 180 has created a monster. Who’s going to fix it, and when?
Direct Revenue Commission Skimming
In my final visit to the CNET Q&A microphone, I mentioned Direct Revenue “skimming off the top” — invoking affiliate commission links to claim commissions on purchases users were already making. I previously documented this same behavior by 180solutions — finding it surprisingly widespread, yet reportedly an easy way to make money. (Last year 180 told MSNBC that it made more than $100,000 from Dell in just one month in late 2003.)
Direct Revenue’s commission-skimming was relatively easy to spot — with telltale signs in users’ cookies folders, not to mention noticeable popunders and, as usual, clear records in packet sniffers. So I was pleased to learn that affiliate network Commission Junction has already noticed this scam and, reportedly, taken action. So perhaps there’s less need for me to post the various videos, screenshots, packet logs, and other proof I’ve been accumulating. Instead, I’ll soon be focusing on reporting DR advertisers — some shocking examples, like American Express ads continuing to target kids sites.

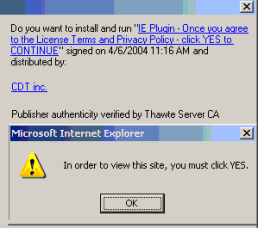
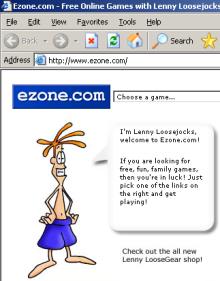 Can we say that a user “consents” to an installation if the installation occurred after a user was presented with a misleading advertisement that looked like a Windows dialog box? If that advertisement was embedded within a site substantially catering to children? If that advertisement offered a feature known to be duplicative with software the user already has? If “authorizing” the installation required only that the user click on an ad, then click “Yes” once? If the program’s license agreement was shown to the user only after the user pressed “Yes”? These are the facts of recent installations of Claria software from ads at games site Ezone.com.
Can we say that a user “consents” to an installation if the installation occurred after a user was presented with a misleading advertisement that looked like a Windows dialog box? If that advertisement was embedded within a site substantially catering to children? If that advertisement offered a feature known to be duplicative with software the user already has? If “authorizing” the installation required only that the user click on an ad, then click “Yes” once? If the program’s license agreement was shown to the user only after the user pressed “Yes”? These are the facts of recent installations of Claria software from ads at games site Ezone.com.

 Screen-shot of my Program Files folder, showing some of the programs installed on my test computer.
Screen-shot of my Program Files folder, showing some of the programs installed on my test computer.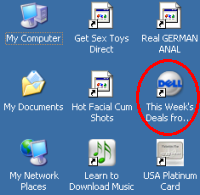 Screen-shot of the icons added to my test computer’s desktop. Note a new link to Dell — an affiliate link such that Dell pays commissions when users make purchases after clicking through this link.
Screen-shot of the icons added to my test computer’s desktop. Note a new link to Dell — an affiliate link such that Dell pays commissions when users make purchases after clicking through this link.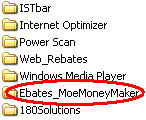 Partial screen-shot taken from video of Ebates installation through a security hole, without any notice or consent.
Partial screen-shot taken from video of Ebates installation through a security hole, without any notice or consent.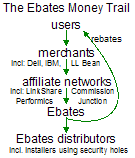 The Ebates Money trail: users -> merchants -> affiliate networks -> Ebates -> Ebates distributors
The Ebates Money trail: users -> merchants -> affiliate networks -> Ebates -> Ebates distributors