Seeking to clean up its image, Claria has tried to distance itself from competing “adware” vendors — hiring a privacy officer, filing comments with the FTC, even setting up an anti-spyware site. It’s no surprise that Claria wants little to do with other vendors in this space: Other vendors’ entirely nonconsensual installations (1, 2, 3) are a magnet for criticism. These vendors even undercut Claria’s pricing — showing ads for as little as $0.015 per display, where Claria demands a minimum payment of $25,000 per ad campaign.
But despite Claria’s dislike of “spyware” vendors who install advertising software without any notion of user consent, Claria funds and supports such vendors in at least two distinct ways. First, Claria pays spyware vendors to show Claria’s own ads through their popups — thereby recruiting more users to install Claria’s advertising software. Second, Claria buys traffic from spyware vendors and uses this traffic to show ads for Claria’s advertiser clients — including merchants as reputable as Amazon.
So even as Claria reforms its own practices — improving its installation methods and scaling back its controversial popups — Claria is buying ads from others whose practices are far inferior.
Soliciting Installations through Spyware-Delivered Popups
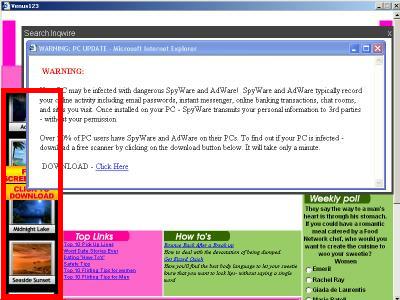 At bottom-left, a Claria screensaver ad shown within a Venus123 popup. The Venus123 popup was opened by ContextPlus, which had become installed on a test PC via a security exploit, without my consent. The Venus123 popup is so large that it entirely covers the test PC’s Start Menu and Taskbar.
At bottom-left, a Claria screensaver ad shown within a Venus123 popup. The Venus123 popup was opened by ContextPlus, which had become installed on a test PC via a security exploit, without my consent. The Venus123 popup is so large that it entirely covers the test PC’s Start Menu and Taskbar.
(promoting installation of Claria “adware”)
money
Zedo.com
(an ad network)
money
02320.net
money
Yieldmanager.com
(an ad network)
money
Venus123.com
money
ContextPlus
(spyware installed without consent)
The money trail — how funds flow from Claria to ad networks to spyware vendors (here, ContextPlus).
I have posted a series of pieces critiquing Claria’s installation methods — showing installations at kids sites, in tricky bundles, with substantively unreasonable license agreements. I haven’t recently seen the fake-user-interface Claria ads I wrote about previously — ads which encouraged users to install Claria by mimicking distinctive Windows dialog box formatting. But I am seeing Claria’s ads embedded within popups delivered by spyware — that is, delivered by advertising software installed on my test PC without my consent.
Consider the screenshot at right, showing the venus123.com site with a Claria screensaver ad at bottom-left. This venus123 ad was delivered to my test PC via ContextPlus spyware, which had become installed without my consent. ContextPlus sent traffic to clickandtrack.net which sent traffic to venus123.com. Then venus123.com embedded an ad from Yieldmanager.com, which in turn send traffic to 02320.net, which embedded an ad from Zedo.com, which finally sent the traffic on to Claria’s belnk.com server.
This ContextPlus-Claria ad display reflects an unusually lengthy series of relationships — summarized in the diagram at right. But the net effect is that Claria makes payments that ultimately flow back to ContextPlus — thereby funding spyware installed without consent. A partial URL log follows below, and I also retained a full packet log.
http://adchannel.contextplus.net/services/…
http://hits.clickandtrack.net/cgi-bin/hit?…
http://www.Venus123.com/homepage.precision…
http://ad.yieldmanager.com/imp?z=0&i=2578&…
http://ad.yieldmanager.com/iframe3?AAAAAAQ…
http://adchannel.02320.net/services/AdChan…
http://c5.zedo.com/jsc/c5/ff2.html?n=350;c…
http://c5.zedo.com/bar/v12-500/c5/jsc/ifra…
http://c4.zedo.com/ads2/d/2077/172/350/355…
http://c4.zedo.com//ads2/k/83990/2077/172/…
http://dist.belnk.com/4/placement/1461/?h=…
A Claria installation obtained through this ad may or may not be “consensual.” To reach a conclusion, we’d have to look at what follows when users click the ad — what they’re told about the advertising, privacy, and other relevant effects of installing Claria’s software. (Perhaps I’ll give these ads a close reading in the future, as I previously did for Claria’s fake-user-interface banner ads at kids sites.) But whether or not users ultimately consent to install Claria’s software, it’s troubling to see Claria using its purchasing power to support spyware installed without user consent.
Showing Advertisers’ BehaviorLink Ads through Spyware-Delivered Popups
 An Amazon ad served through Claria BehaviorLink within a popup from Savings-card.com. The Savings-card.com popup was opened by KVM Media, which had become installed on my test PC via a security exploit, without my consent.
An Amazon ad served through Claria BehaviorLink within a popup from Savings-card.com. The Savings-card.com popup was opened by KVM Media, which had become installed on my test PC via a security exploit, without my consent.
(and other BehaviorLink advertisers)
money
Claria BehaviorLink
money
Savings-Card.com
(and other sites buying traffic from spyware vendors)
money
KVM Media
(spyware installed without consent)
The money trail — how funds flow from advertisers (here, Amazon) to spyware vendors, via Claria’s BehaviorLink service.
Claria’s funding of spyware (installed without consent) extends beyond Claria’s methods of obtaining new users for its software. Claria also purchases spyware-originated traffic on behalf of its advertiser customers.
In February 2005, Claria announced its new BehaviorLink advertising network. Unlike the controversial pop-ups of Claria’s GAIN — which have brought litigation from web publishers unhappy to see their sites covered by competitors’ popups — BehaviorLink will show ads within publishers’ sites, paying those publishers a share of Claria’s revenue. Viewed in the most favorable light, BehaviorLink would fund free software users want and would help support the sites users request — a winning offer for both users and web sites, Claria claims.
Is the truth as rosy as Claria’s promises? On some level it’s hard to know: Claria’s BehaviorLink says the service is in a “pilot,” and so far we’ve heard little from participating advertisers and publishers. Perhaps it’s too soon to say how well BehaviorLink will work.
But in my initial examination of BehaviorLink traffic, I see serious cause for concern. In particular, I have found that Claria is buying BehaviorLink ad inventory from web sites that receive traffic directly from some of the most notorious spyware, including spyware installed on users’ computers without notice or consent.
Consider the example at right. Savings-card.com buys traffic from KVM Media, which I have repeatedly observed install without notice or consent. So as users browse the web, KVM opens popups of Savings-card.com. But Savings-card.com, which in turns redirects users to Claria’s BehaviorLink. BehaviorLink them shows an ad from one of its partners. The example below at right shows an Amazon ad placed through BehaviorLink, arriving in exactly this way. See also a screenshot of the result of activating the View-Source menu command in the Savings-card popup. Below is a partial URL log showing traffic leading to the ad and (in the final entry) the result of clicking on the ad.
http://www.icannnews.com/cgi-bin/PopupV3?ID=…
http://www.savings-card.com/normal/yyy99.html
http://dist.belnk.com/4/placement/1968/
http://ath.belnk.com/placement/?cb=6747118&did=269085&pid=1968&mint128=343…
http://art.ath.belnk.com/4/creative/42514.1/content42514-0.html?at2=2&imp=…
http://www.amazon.com/exec/obidos/redirect?link_code=ure&camp=1789&tag=ce-…
Note that this popup appeared on a PC without BehaviorLink (or any other Claria software) installed. BehaviorLink’s web servers selected the Amazon ad randomly or on the basis of my other browsing on this test PC.
Claria’s Spyware-Delivered Advertising in Context
Claria’s own comments with the FTC concede that “spyware” is “illegal” under existing law to the extent that such software “is installed [on a consumer’s computer] without the consent of the consumer.” I agree. So Claria must be disheartened to find its ads and its clients’ ads shown through precisely this concededly-illegal software. I doubt that Claria intended to buy spyware-delivered advertising traffic. But by buying the cheapest available advertising space, Claria invited this result. Indeed, Claria’s BehaviorLink business model is premised on buying low-quality ads. Claria’s Scott Eagle told the New York Times in February: “We’ll take ad inventory that costs 50 or 75 cents, buy it in bulk, and turn it into gold by targeting $6 or $15 precision ads there. We’ll be the alchemists.” (cached copy)
To date, BehaviorLink has received strikingly positive press coverage. The media has largely accepted Claria’s promises — advertising software installed because users actually want it (not because they were tricked into accepting it, see above), and ads shown within high-quality partner web sites (not spyware-delivered popups). On the strength of these promises, it seems that Claria has been able to recruit remarkably high-quality advertisers like Amazon — advertisers who would not want to be associated with Claria’s traditional pop-ups.
My observations lead me to challenge these favorable assumptions about BehaviorLink. I still doubt whether users will install Claria’s software if Claria fully discloses the consequences of doing so (especially the effects on privacy). And the KVM Media example above shows BehaviorLink’s dependence on the quality of sites showing BehaviorLink ads. If Claria buys traffic from spyware vendors, directly or indirectly, then BehaviorLink ads get placed in spyware-delivered popups, not in web sites users actually want to visit. Then BehaviorLink ends up funding spyware, not funding the web sites users request.
Avoiding spyware-sourced traffic will require exceptional diligence on Claria’s part — inevitably driving up costs and reducing the profit margins Scott Eagle touted to the Times. I already have several more examples of BehaviorLink ads delivered in popups from exploit-installed spyware, and I’ll be watching for more.
Of course Claria is not the only network facing the problem of spyware-delivered ads. In May I examined more than 88,000 ads then served by 180solutions, finding that literally thousands flowed to or through major ad networks such as aQuantive’s AtlasDMT. These bogus syndication relationships remain widespread, as to popups served by 180solutions and numerous others. I’ve written a series of crawlers and robots to help me assess these problems — identifying which ad networks are involved, and identifying specific ad URLs that are affiliated with spyware vendors. But it’s a remarkably deep problem: Ads are passed from one ad network to another in ways that tend to confuse even my smartest crawlers. And ad networks have little incentive to investigate or stop these practices: They can only lose revenues by prohibiting such ads, so most networks seem to prefer to look the other way.
For now, spyware-delivered popups continue to promote many of the world’s leading merchants — including, thanks to Claria’s BehaviorLink, Amazon.com.