I’ve long been a fan of online shopping site Ebates. Sign up for their service, visit their web site, click through their special links to merchants (including merchants as distinguished as Dell, Expedia, IBM, and L.L. Bean), and earn a small cash back, generally a few percent of your purchase.
But another side of Ebates’ business has become controversial: Ebates uses a software download called “Moe Money Maker” (MMM) to automatically claim merchants’ affiliate commissions, then pay users rebates — even if users don’t visit Ebates’ web site, and even if users don’t click through Ebates’ special links.
Why the controversy? I see at least two worries:
1) Aggressive software installations.
-
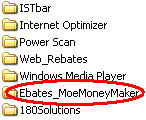 Partial screen-shot taken from video of Ebates installation through a security hole, without any notice or consent.
Partial screen-shot taken from video of Ebates installation through a security hole, without any notice or consent.Users visiting ebates.com can receive MMM software merely by filling out a form and failing to uncheck the “I would like to download MMM” checkbox (checked by default).
- Users downloading certain third-party programs (screen-savers and the like) receive MMM as part of the bundle — disclosed, in my testing, but often with a long license in a small box, such that many users don’t fully understand what they’re getting.
- Most troublingly, there have been persistent allegations of Ebates installed without any notice or consent whatsoever. I had always discounted these allegations until I saw the proof for myself earlier last month. See video of Ebates MMM installed through security holes.
2) Claiming affiliate commissions that would otherwise accrue to other affiliates. Many web sites receive affiliate commissions when users make purchases through special links to merchants’ web sites. (See e.g. Lawrence Lessig‘s “Get It Here” page.) Network rules (Commission Junction , Linkshare) prohibit Ebates from interceding in these transactions; instead, the independent web sites are to receive the commissions for purchases through their links. But Ebates’ software sometimes claims commissions anyway — specifically contrary to applicable rules. These behaviors have been alleged and reported for years, and recently documented in a series of videos (videos of particular interest. Apple, Cooking.com, Diamonds International, JJill, Lillian Vernon, Sharper Image, Sony). If Ebates’ prohibited interventions were only temporary, they would be easy to sweep away as mere malfunctions. But when problems continue for years, to Ebates’ direct financial benefit and to others’ detriment, the behavior becomes harder to disregard.
Meanwhile, Ebates has inspired copy-cat programs with similar business models but even more controversial execution. I’ve recently made literally scores of videos of eXactAdvertising‘s CashBack by BargainBuddy installed through security holes, and also of TopRebates/WebRebates installed through security holes — always without any notice or consent whatsoever. These programs remain participants in the Commission Junction and LinkShare networks — presumably receiving commissions from these networks and their many merchants (CashBack merchants, TopRebates merchants). I’m surprised that so many merchants continue to do business with these software providers — including so many big merchants, who in other contexts would never consider partnering with software installed without notice and consent.
I think the core problem here is skewed incentives. Affiliate networks (CJ and LinkShare) have no financial incentive to limit Ebates’ operation. Instead, the more commissions claimed by Ebates, the more money flows through the networks — letting the networks charge fees of their own. In principle we might expect merchants to refuse to pay commissions not fairly earned — but merchants’ affiliate managers sometimes have secondary motives too. In particular, affiliate managers tend to get bonuses when their affiliate programs grow, which surely makes them particularly hesitant to turn away the large transaction volume brought by MMM’s automatic commission system. That’s not to say some merchants don’t knowingly and intentionally participate in Ebates — some merchants understand that they’ll be paying Ebates a commission on users’ purchases even when users type in merchants’ web addresses directly, and some merchants don’t mind paying these fees. But on the whole I worry that Ebates isn’t doing much good for many merchants, even as its software comes to be installed on more and users’ PCs, with or without their consent.
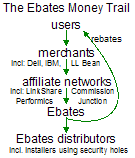 The Ebates Money trail: users -> merchants -> affiliate networks -> Ebates -> Ebates distributors
The Ebates Money trail: users -> merchants -> affiliate networks -> Ebates -> Ebates distributorsFor users who share my continued interest in following the money trail, the diagram at right summarizes Ebates’ complicated business model. Users make purchases from merchants, causing merchants to pay affiliate commissions (via affiliate networks such as LinkShare and Commission Junction) to Ebates. Ebates in turn pays commissions to those who cause its software to be installed, including those installers who install Ebates’ software through security holes, without notice or consent.
Ebates Terms & Conditions Allow Removing Other Programs
Finally, note that Ebates has joined the ranks of software providers who, in their EULAs, claim the right to remove other software programs. Ebates’ MMM Terms & Conditions demand:
“Ebates may disable or uninstall any other product or software tool that might interfere with the operability of the Moe Money Maker Software or otherwise preempt or render inoperative the Moe Money Maker Software … In installing the Moe Money Maker Software, you authorize Ebates to disable, uninstall, or delete any application or software that might, in Ebates’ opinion nullify its function.”
Ebates is right to worry that a user can only successfully run a single automatic commission-claiming program. But this license language allows Ebates to delete far more than competing commission programs. For example, if Ad-Aware removes MMM as spyware, thereby “interfering with the operability” of MMM, then the license purports to give Ebates the right to remove Ad-Aware.
Update (December 15): Ebates staff wrote to me to report that they have narrowed the clause quoted above. Ebates’ current Terms allow disabling only “shoping or discount software,” not general-purpose software removal tools like Ad-Aware. Ebates staff further note that they have never exercised the rights granted under the prior Terms text. However, Archive.org reports that Ebates’ Terms included the broad “any application or software” language as long ago as August 2003.
Thanks to Ian Lee, Internet Marketing Strategist & Affiliate Manager of ADS-Links.com, for recommendations on video production methods.